You may think that How To Bypass Two Factor Authentication (2FA), all of your employees are safe.
While 2FA is among the simplest ways to feature a further layer of security on top of user credentials, it can still be bypassed. we’ll show you ways easy it is often to avoid it.
Just last Fall, the FBI warned the general public about the rising threat against organizations and their employees and how standard social engineering techniques are wont to bypass 2FA.
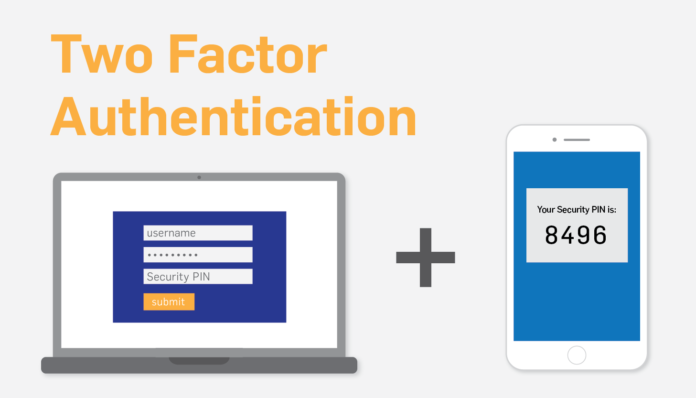
What is two-factor authentication?
Two-factor authentication is employed on top of the user’s password when logging into an account as a second authentication. The second layer of authentication is often a code provided through text message, authenticator applications, or it is usually made from a fingerprint or face recognition.
Two-factor authentication may be a subset of multi-factor authentication. Within the case of multi-factor authentication, the user is required to spot himself/herself in additional than two alternative ways.
How does two-factor authentication work?
Two-factor authentication always requires a second sort of identification. Once you attempt to log in to an account, first, you want to enter your username and password.
When the two-factor authentication is enabled, you’ll get to provide a second sort of proof that you are the owner of the account before you’ll access it.
Why do you need two-factor authentication?
Two-factor authentication is another layer of security. Albeit you mistakenly gave away your password, hackers would wish to urge access to the second sort of identification before they might enter your account.
It’s strongly recommended that you activate two-factor authentication for any essential account if possible. It’s an additional layer of security that keeps you always secure.
Unless, of course, you fall victim to social engineering, and you divulge the two-factor authentication code yourself.
If you’re trying to find an authenticator application, here are some smartphone apps you’ll consider:
- Google Authenticator
- Microsoft Authenticator
- Salesforce Authenticator
- SecureAuth
- Duo Security
- Symantec VIP
- Transakt
- LastPass Authenticator
How hackers are using social engineering techniques to bypass two-factor authentication
While organizations consider two-factor authentication a secure way of identifying access, there are relatively simple techniques for bypassing 2FA.
In most cases, we assume that the attackers have already got the user’s password.
1. Bypassing 2FA with conventional session management
In this case, attackers use the password reset function because, often, 2FA isn’t implemented on the system’s login page after a password reset.
How does it add practice?
- The attacker clicks on the ‘change password’ link.
- The attacker requests the password reset token.
- The attacker uses the password reset token.
- The attacker logs into the online application.
Using this method, attackers can bypass the two-factor authentication in specific platforms where the architecture of the location or platform makes it possible.
2. Bypassing 2FA using OAuth
OAuth integration allows users to log into their account employing a third-party account. This suggests that you would have an alternate choice to sign into a platform together with your Facebook or Gmail accounts.
How does OAuth work?
- The site requests an authentication token from the third-party site (e.g., Facebook).
- Facebook (or another third-party site) verifies the user account.
- Facebook (or another third-party site) sends a callback code.
- The site logs the user in.
Here, the attackers don’t even get to use 2FA if they, for instance, have the user’s Facebook or Gmail username and password.
3. Bypassing 2FA using brute force
When the length of the two-factor authentication code is four to 6 characters (often just numbers), it makes it possible for attackers to bypass 2FA by using brute-force against the account.
4. Bypassing 2FA using earlier-generated tokens
Some platforms offer users the likelihood to get tokens beforehand, like a document with a particular number of codes, to be used later for bypassing 2FA.
If an attacker gets access to the document, they will easily use it to bypass 2FA, assuming that they even have the user’s password.
5. Bypassing 2FA using social engineering
Case 1
In this case, we assume that the attacker features a hold of the user’s username and password.
To attain the 2FA code, the attackers could send an email to you with a made-up excuse to request the verification code sent to your number. Once you send them the code, the attacker is going to be ready to bypass the 2FA.
Case 2
Even when the attackers don’t have your username and password, they might bypass 2FA by getting you to click on a link and attend a phishing website that mimics a genuine website, like LinkedIn. the email would appear as if it comes from the service provider itself.
When you provide your login credentials on the fake page, the hacker can check in on the critical website. At that time, you receive a code, and once you enter it on the fake website, the hacker gets the code also. They will then successfully breach your account.
Stay safe when using 2FA
Despite the issues that we outlined above, two-factor authentication remains an excellent thanks to secure your accounts.
Here are a few recommendations on the way to stay safe while using two-factor authentication:
- Use authenticator apps like Google or Microsoft Authenticator whenever possible rather than text message codes.
- Never share security codes with anyone.
- If possible, use codes with characters of quite 4 to six.
- If you’re unsure about your security, double-check with somebody else about what you ought to do.
- Use complex passwords – use a password generator and a password manager.
- Never reuse passwords.
- Consider using a security key as an alternate sort of authentication utilized in 2FA.
- Care about your security and understand common social engineering tactics.