Cybersecurity Playbook Example
What is a Cyber Security Playbook?
Nearly All organizations aim such as fires, flooding, and others. The episode that affects company durability and cautious preparation...
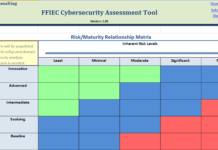
ffiec Cybersecurity Assessment Tool xls
we created and posted a ffiec Cybersecurity Assessment Tool xls into action by tracking your responses
Overview for Chief Executive Officers and Boards of Directors
In light...
Report Cyber Crime Australia
Here we can see, "Report Cyber Crime Australia"
What is ReportCyber?
On 30 June 2019, the ACIC's Australian Cybercrime Online Reporting Network (ACORN) system transitioned to...
Cybersecurity VARs
Directory of Cybersecurity VARs and Systems Integrators
Cybersecurity Ventures is on a particular project compiling a searchable database of Cybersecurity VARs and SIs within the...
Australian Security Commission
Here we can see, "Australian Security Commission"
Australian Securities and Investments Commission (ASIC)
ASIC is currently Australia's corporate, markets, and financial services regulator.
ASIC contributes to Australia's...
Cybersecurity Lifecycle
Whether you are a small, midsize, or large company, a Cybersecurity Lifecycle can be costly and even deadly to your company's survival. A good...
Programming Languages For Cyber Security
Here we can see, "Programming Languages For Cyber Security"
What is cybersecurity?
Cybersecurity could be explained as the collective procedures, technology, and procedures to protect the...
Australian Cyber Security Centre
Here we can see "Australian Cyber Security Centre" following the given content.
What is cybersecurity?
Cybersecurity includes the security of computer systems linked to the world...
Cybersecurity Risk Assessment
What is a Cybersecurity Risk Assessment?
Cybersecurity Risk Assessment is characterized by NIST as dangers assessments are utilized to identify, quote, and reevaluate hazards to...
Red Team Exercise Cybersecurity
What is a red team
In a Red Team Exercise Cybersecurity simulation, this red group functions as an adversary, recognizing and exploiting potential weaknesses in...